Archive
6 Essential Tips on How to Prevent Online Shopping Fraud
Dear readers and followers, I would first like to wish you a very Happy New Year, good health and great personal and professional accomplishments.
As some of you have already purchased products/services online (and I would like to invite you to share your experience with us) and some others will have at a some point, I am featuring today Israel Defeo as guest blogger on this common topic: Online shopping.
Shopping online is easy. You get what you want in a matter of seconds. Just input your credit card information and voila, that book or jacket or bag is already on its way to you within 24 hours.
This is why more shoppers are switching to e-stores and e-transactions—e-payments, e-banking—are fast becoming the norm. Convenience is the ultimate game-changer. Plenty of online shops, too, offer discounts and freebies like free delivery or free shipping.
However, the rise in e-transactions has also made online fraud possible. To prevent online shopping fraud from happening to you, here are some easy tips you can follow:
1. Keep your credit details a secret.
Like the famous quote said, “There are things better left unsaid.” That may be true especially if it’s about your credit, debit or other essential information that need to be kept secret.
2. Use caution when using your devices for online shopping.
Because it’s more convenient to shop online using smartphones, tablets, and other mobile devices with internet access, more consumers prefer to use these gadgets than computers and laptops—which are more secure. Beware of using your handheld devices for transactions that carry your personal and credit card information. In case your device is misplaced or lost, you’re at risk of falling victim to fraudsters and scammers who can extract your private information through the lost device.
3. Beware of phishing websites.
Have you ever seen items on some websites offered at very low prices? Though it can be tempting to purchase low-priced bargain items, it can also come at great risk to the safety of your credit and personal details.
There are internet criminals who create phishing or fraudulent websites which trick you into signing up and disclosing your private information. Some of these websites duplicate the content and design of legitimate ones to fool shoppers like you into revealing their credit card details. At this point, it may be better for you to let common sense—or your gut feel—rule. If you feel like the price is unbelievable or a deal sounds too good to be true, chances are, it is. Stay away from fishy-looking sites as much as possible to keep from being a victim of identity theft.
4. Verify if the website is legitimate or not.
Remember, Google is your friend. This search engine can help you find any information you need to get your hands on. Search for the name of the website and see if there’s anything involving “scam” or “fraud” mentioned in blogs, forums or other online sources.
5. Don’t click hyperlinks from random emails.
You probably received not just one, not just two, but more emails about offers and discounts about a product or service in your email. Be mindful of clicking links attached to those messages because it may redirect you to fraudulent websites or phishing sites. Also beware of attachments you receive from untrusted sources. These may contain viruses and malwares that may not just harm your electronic devices, but can also swipe information from your units.
Sometimes, web mail servers can filter unreliable messages and put these messages in the Spam folder of your email. So make sure this feature is enabled in your settings.
6. Beware of bogus sellers lurking in social media sites
Social media sites are also used by small-scale entrepreneurs to market their products and promote their services to a wider audience. It has been an advantage to both sellers and buyers because Facebook, Twitter, Instagram and other social media platforms can be used for easy communication, placing orders, and completing transactions because it allows real-time responses.
However, scammers can easily post photos and create bogus accounts about bogus products or services. So be mindful of the sellers you buy from. If they cannot ship or send the product they promised after a transaction, you may have already been scammed. To avoid this fate, make sure to call up the seller before you even buy anything. If you smell or hear something fishy or that makes your antennae quiver in suspicion, go and search for another seller until you find one you can trust.
So be careful whenever you use your credit card. Follow the tips mentioned above to help you make sure your credit card and credit information are both safe—and to keep online fraud from happening to you.
This guest post is written by Israel Defeo. He is the writer and online promoter of the leading financial comparison website in Hong Kong, Money Hero. The online portal presents up-to-date and unbiased information about insurance companies, credit cards, loans, deposit accounts and broadband and mobile plans.
Any questions can be submitted to: dan@e-crimeexpert.com
Additional information can be found at: http://www.e-crimeexppert.com
To find out more about Dan Manolescu, visit his LinkedIn page here.
Hit the “subscribe” button in order to be notified when new videos and Articles are posted on this blog
10 Ways to Prevent Your Identity From Being Stolen
Today, we welcome our guest Amanda Kostina who is a green living enthusiast and a blogger for withefence.com. She generally writes about green lifestyles, eco-friendly businesses, and frugal living. Amanda is always passionate about making the world a better place for the generations ahead.
Bellow, you can read Amanda’s interesting guest post on how to prevent identity theft.
One of the fastest growing crimes in the United States, identity theft affects millions of Americans. From phishing scams to taking advantage of the information in a lost or stolen wallet, criminals have a variety of options when it comes to methods of exploiting your information for their own gain. Fortunately, there are also a few simple steps you can take to protect yourself against their nefarious efforts, maintaining control over your own identity and preventing it from being stolen.
1.Clean Out Your Wallet – Many people keep their Social Security cards on their person for easy access, but this practice can easily put one of your most sensitive pieces of personal information into the hands of identity thieves if your wallet is stolen or becomes lost. Make a point of storing your Social Security card in a safe place other than your wallet, and of periodically clearing out any bits of paper bearing sensitive information.
2.Come Up With Creative PIN Numbers – Choosing your wedding anniversary or the birth date of a child for account pin numbers makes them easy to remember, but it also makes them relatively easy for would-be identity thieves to guess. A jumble of numbers or letters that have no connection to one another is ideal, as the random nature makes them much more difficult to suss out.
3.Memorize PIN Numbers – The major selling point of using an important date or significant number as the PIN on a financial account is ease of memorization, but that also makes them easy to guess. When you do come up with a secure PIN, don’t write it down and leave the slip of paper in your wallet or on your person, as that information would fall into the hands of an identity thief right along with the card it’s attached to if your wallet is ever stolen. Take the time to memorize the number instead.
4.Check Your Mail – Letting your mail pile up while you’re on vacation or simply forgetful can leave you with more than just a clogged mailbox. It can also up the chances of documents containing sensitive information being taken by an unscrupulous passerby. Make sure that you’re clearing the mailbox every day, or that you make arrangements for the postal service to hold your mail while you’re traveling.
5.Invest in a Document Shredder – Dropping sensitive documents into a shredder is the work of a moment, and it makes it much more difficult for criminals to steal discarded papers from your garbage can or recycling bin with sinister aims.
6.Monitor Account Activity – Opting out of paper statements from your bank and other financial institutions not only keeps your statement out of the mailbox, but also helps you to do your part for the environment by eliminating a bit of unnecessary paper use. Instead, check your statements and monitor activity online. You’ll be able to keep an eye on your account any time you like, and you won’t be leaving personal information on a statement that’s up for grabs to any thief in the area.
7.Check Your Credit Report Annually – By federal law, you are entitled to one free credit report each year. It’s wise to take advantage of that right, not only to keep an eye on your rating, but also to check for signs of old identity theft or fraudulent activity.
8.Install Anti-Virus Software – Your computer makes paperless billing and statements available, allows you to conduct transactions from the comfort of your home and is an indispensible tool for the modern American. Without proper anti-virus and security software, it’s also an open invitation for identity theft and fraud. Make sure that you’re running up-to-date and reliable software to protect your PC, too.
9.Be Cautious Online – Whether you’re looking for work online or applying for financing, there are a wide variety of helpful tools to be found on the Internet. Unfortunately, there can also be a minefield of potential issues for those who aren’t cautious in their online dealings. Make sure that you’re only sharing sensitive information with reputable sources.
10.Practice Smart Phone Strategies – Unless you initiated a phone call and are sure you’ve reached the intended party, it’s wise to make a practice of never providing personal information over the phone. This especially holds true with unsolicited sales or marketing calls, because you can’t always be sure that the person on the other end of the line is a legitimate representative. To be safe, decline any offers that would require the sharing of your social security number, financial account details or other sensitive information.
Source: Amanda Kostina for: whitefence.com
To view the original Post click here.
Any questions can be submitted to: dan@e-crimeexpert.com
Additional information can be found at: http://www.e-crimeexppert.com
To find out more about Dan Manolescu, visit his LinkedIn page here.
Hit the “subscribe” button in order to be notified when new videos and Articles are posted on this blog
How to download your own data from Facebook
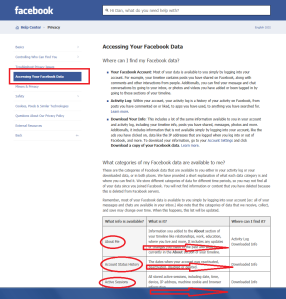
From the same series on how to access, delete, download, transfer your data when using a major Online Social Service (Facebook) or email Provider (i.e. Google, Yahoo), today E-Crime Expert explains how a user can have access and also download his/her data Facebook collects and keeps under that particular user account.
Follow the steps bellow if you would like to have access to the data Facebook holds under your account:
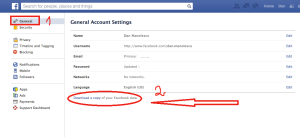
1. Log on Facebook and access the “Settings” tab. From there, click on the “Account settings” from the drop-down menu (Fig. 1).
Fig. 1.
2. Navigate to the “General Account Settings” tab and click on the “Download a copy of your Facebook data” (on the bottom of the page). Fig. 2.
Fig. 2.
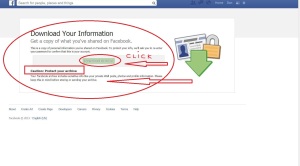
3. You will be promoted with a message that enables you to download your data. Also, Facebook warns the users in regards to the sensitive character of the data under their personal Facebook account. Think twice before downloading your data if you do not trust the computer you are using (i.e. Public Library, etc.). If you do trust it, just click the “Download archive” button in order to get access to your data. Fig. 3.
Fig. 3.
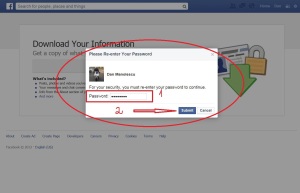
4. Next, you will need to type your password again, even though you are logged into your account (for security reasons). After typing your password, click on the “Submit” button. (Fig. 4).
Fig.4.
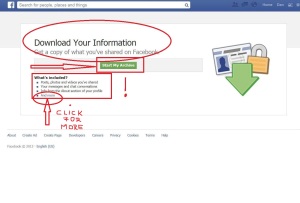
5. Again, a message is displayed informing the user which data will be downloaded: Pictures, archives, messages, timeline posts, AND MORE! (Fig. 5).
Fig. 5.
6. Also, you can manually chose to select what data you would like to download such as: photos, messages, videos, etc. For this, click here and you will be automatically redirected to another page where you could select what data you want to download (Fig.6). Or you could also click on the “And more” tab as shown in Fig.5 above.
Fig.6.
7. Now, depending on your Operating System (i.e. Windows or Apple), or your Browser (i.e. Internet Explorer or Safari) and also on the time elapsed since you last requested your data from Facebook (if ever), your data will either start downloading immediately to your computer or it will be sent to the email address associated with your Facebook account. We are explaining bellow both possibilities:
I. Data starts downloading immediately.
After clicking the “Submit” button (see Fig. 4 above), you will be prompted to save your data on your computer. Chose a location you are familiar with and also which it is neither public nor shared with other users and click “Save”. Your data will start downloading automatically. (Fig.7).
Fig.7.
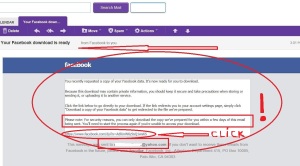
II. Data is sent to the email address associated with your Facebook account.
You will be prompted with another message called “Start my archive”. Click on it. (Fig. 8).
Fig.8.
-The email address associate with your Facebook account is displayed in order for the user to confirm that this is the right email address. If so, click on “Okay”. (Fig. 9).
Fig.9.
-Check your Inbox folder (under your email account) and click on the message received from Facebook. On the bottom of the message you will find a link similar to this: https://www.facebook.com/joe.doexfnr11……..Qdxwe…..rlaA9LVP. Click on it. (Fig. 10).
Fig.10.
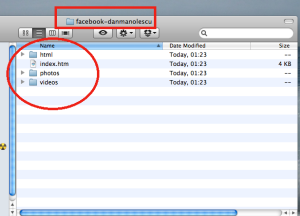
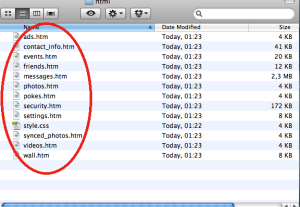
-Again, be careful and chose a location you are familiar with and also which it is neither public nor shared with other users and click “Save”. Your data will start downloading automatically. The folder with your Facebook data will look like in the pictures bellow. (Fig. 11 and 12).
Fig. 11.
Fig.12.
Any questions can be submitted to: dan@e-crimeexpert.com
Additional information can be found at: http://www.e-crimeexppert.com
To find out more about Dan Manolescu, visit his LinkedIn page here.
Hit the “subscribe” button in order to be notified when new videos and Articles are posted on this blog
How to: Deactivate, Delete, Memorialize or Remove a Facebook account
Continuing a series started this summer about how Google (original post here) and Yahoo users (original post here) could control their data, E-Crime Expert presents today how Facebook users could control their data by having their accounts deactivated, memorialized or deleted.
Facebook does not disable profiles if they are not being actively used as Yahoo does.
The only way a Facebook account closes is if the user chooses to disable it (deactivate or delete); or when a family members for example (i.e. of a deceased account holder) requests the memorializing or removing of an account; or as a result of a breach of Facebook terms and policies.
1. Deactivate your account
1) Log on your Facebook account, click on the “Settings” pictogram (step 1) and then select “Account settings” (step 2) from the drop-down menu (Fig. 1).
Fig. 1
2) Chose the “Security” (step 1) tab on the left side menu (then “Security settings” will display on the right), go to the bottom of the “Security settings” menu where you’ll see the “Deactivate your account” button (Fig.2). Click on it (step 2).
Fig. 2
3) A new page will be displayed, chose one of the reasons you are disabling your account (Step 1), check the “Opt out” box if you do not want to further receive emails from Facebook (Step 2) and then click on “Confirm” (Step 3). Fig. 3.
Fig. 3
4) A pop-up Notification will appear prompting you (for security reasons) to introduce your password (Step 1). After introducing your password click on the “Deactivate Now” button (Step 2) as described below in Fig. 4.
Subsequently, your account will be deactivated.
Fig. 4
When you deactivate your account, your timeline and all information associated with it disappears from Facebook immediately. People on Facebook will not be able to search for you or view any of your information.
If you’d like to come back to Facebook anytime after you’ve deactivated your account, you can reactivate your account by logging in with your email and password. Your timeline will be restored in its entirety (friends, photos, interests, etc.). You will need to have access to the login email address for your account in order to reactivate it.
2) Delete your account
Directly click on this link.
Or follow the steps bellow if you are not logged in your Facebook account:
1) Log on your Facebook account, clcik “Settings” (Step 1) and then click on “Help” (Step 2) from the drop-down menu (Fig.5).
Fig. 5
2) Type in the search box (Step 1): “Delete my account” and then click on the “How do I permanently delete my account” (Step 2) link from the options displayed in the drop-down menu (Fig.6).
Fig. 6
3) A new menu will open where you need to click on the “Fill out this form” (The red box illustrate in Fig. 7)
Fig. 7
4) The last step requires you to click on “Delete My Account” button displayed (Fig.8).
Fig. 8
Permanently deleting your account means you will not ever be able to reactivate or retrieve any of the content or information you’ve added. Your account will be permanently deleted with no option for recovery.
3) Memorializing Accounts
When a person passes away, Facebook memorialize their account to protect their privacy. Here are some of the key features of memorialized accounts:
• No one can log into a memorialized account and no new friends can be accepted
• Depending on the privacy settings of the deceased person’s account, friends can share memories on the memorialized timeline
• Anyone can send private messages to the deceased person
• Content the deceased person shared (ex: photos, posts) remains on Facebook and is visible to the audience it was shared with
• Memorialized timelines don’t appear in People You May Know and other suggestions
If you need to report a timeline to be memorialized, please contact Facebook here.
And follow the 5 steps bellow (Fig. 9)
1. Link to the timeline of the person you submit the request for;
2. Insert the email address of the account you submit the request for;
3. Indicate your relationship status with that person;
4. Insert a link to a public/private commemoration of the deceased person (i.e. obituary or news). Please consider to NOT upload videos or pictures;
5. Click on memorialize account.
Fig. 9
4) Removing the account of a deceased person
Verified immediate family members may request the removal of a loved one’s account from Facebook by clicking here.
In order to complete this process, follow the 9 steps bellow (Fig. 10):
1. Introduce your full name;
2. Introduce the full name of the deceased person;
3. Introduce the email account (linked to their Facebook account) of the deceased person;
4. Introduce the web address of their timeline like this: https://www.facebook.com/john.doe
! Replace the john.doe example with the name of your deceased friend.
5. Indicate your relationship to that person;
6. Click on the “Please remove the account” field.
7. Indicate the year when that person passed away;
8. Make proof of your relationship with the deceased by uploading a death certificate or similar;
9. Last step: click “Send”
Fig. 10
Any questions can be submitted to: dan@e-crimeexpert.com
Additional information can be found at: http://www.e-crimeexppert.com
To find out more about Dan Manolescu, visit his LinkedIn page here.
Hit the “subscribe” button in order to be notified when new videos and Articles are posted on this blog
iOS7 Security issues give access to your photos and more
E-Crime Expert brings once again to your attention a security issue, thanks to Jose Rodriguez, from Canary Islands which has found this iOS7 Security glitch that gives access to your photos, and enables the sharing of them via Twitter, Mail, Flickr, Message.
The following demo, pictures and testing is done entirely by E-Crime Expert (Dan Manolescu) on one of our devices. This security issues apply to any Apple device (iPhone, Ipad) that runs on iOS7.
How it works:
From the locked screen menu (Fig.1), pull the “Control center” tab up (Fig.2) and click the “Clock” pictogram (Fig.3)
Fig.1
Fig.2
Fig.3
Then, press the “sleep button” until “turn off your device” (Fig.4) message appears. Instead, press “cancel” and right after double click the Home button (Fig.5).
Fig.4
Fig.5
The “Multitasking” screen will appear (Fig.6). You can now chose the “Camera” app from there and click the “Camera roll” (Fig.7) and you will instantly have access to your photos (Fig.8).
Fig.6
Fig.7
Fig.8
From here, you can share them via Twitter, Facebook, Mail, Flickr (Fig.9).
Fig.9

In order to avoid this security glitch, update your iOS:
Go to “Settings” (Fig.10), then to “General” (Fig.11) and after to “Software update” (Fig.12).
Fig.10
Fig.11
Fig.12
Done Deal!
Again, credit goes to: Jose Rodriguez, from Canary Islands (Spain).
Any questions can be submitted to: dan@e-crimeexpert.com
Additional information can be found at: http://www.e-crimeexppert.com
To find out more about Dan Manolescu, visit his LinkedIn page here.
Hit the “subscribe” button in order to be notified when new videos and Articles are posted on this blog.
Yahoo deletes IDs of inactive email accounts starting with July 15!
E-Crime Expert recently launched a series (see the first blog post here) on how you control your data stored online by different (e-mail) Service Providers. This could be done directly (by setting up an inactive account deletion time for your Google account) or indirectly (by not signing in your Yahoo account).
For those who have a Yahoo account and who have not signed in for the past year, their personal data stored under their account will be automatically deleted with no opportunity to recover it or to transfer it to anyone else by expressing their WILL as Google provides for example by offering the Inactive Account Manager tool.
Warning!
If you are not planning to have your account deleted and all your data erased (emails, pictures, chats, etc), please note that Yahoo Inc. plans to release the inactive accounts unless the current owner logs on again before July 15 (2013). After that, the (deleted) identifications will be available to all comers (as a fresh Yahoo account) and will be ready to use again in mid-August, while the data of the original user will be permanently erased!
Yahoo is resetting email accounts that have not been used for at least 12 months and issuing them to other users as they are trying to attract new users (by freeing unused email accounts) and retain current active users with IDs of their choice, the company is also giving inactive users the opportunity to retain them:
“All you have to do is log on to any Yahoo! product before July 15th. In future, these accounts will remain active by signing in at least once every 12 months, according to a Yahoo help notice, titled “We want you back.”
According to the above statement, All you have to do is log on to any Yahoo! product before July 15th, if you haven’t logged into Yahoo! for over a year, but want to keep your Yahoo! ID, and/or to log on any Yahoo! product at least once every 12 month if you want to keep your Yahoo! account active!
Any questions can be submitted to: dan@e-crimeexpert.com
Additional information can be found at: http://www.e-crimeexppert.com
Hit the “subscribe” button in order to be notified when new videos and Articles are posted on this blog
How to control your electronic assets when you become inactive: Google
E-Crime Expert starts today a series that enables users to manage their online data (electronic assets) if they become inactive (i.e accident, jail time, passed away, etc). Let’s say this is a WILL (testament) for electronic assests which is similar in scope to a WILL for material assests (i.e. house, boat, car, etc).
Google has a program called Inactive Account Manager, that allows those who use Google services decide exactly how they want to manage their online data stored with the company (i.e. Gmail, Picasa, YouTube, blogs, Wallet, etc).
What should happen to your photos, emails and documents when you stop using your account? Google puts you in control.
You might want your data to be shared with a trusted friend or family member, or, you might want your account to be deleted entirely. There are many situations that might prevent you from accessing or using your Google account. Whatever the reason, Google gives you the option of deciding what happens to your data.
Using Inactive Account Manager, you can decide if and when your account is treated as inactive, what happens with your data and who is notified.
i. How to set up your Inactive Account Manager
First, go to https://www.google.com/settings/account
Then, go to the bottom of the page to “Learn more and go to setup” (fig. 1)
Fig. 1
You set a timeout period, after which your account can be treated as inactive. The timeout period starts with your last sign-in to your Google account. Click Setup (fig 2).
Follow the instructions in the picture bellow (fig. 3).
Fig. 3
iii. Alert me
Inactive Account Manager will alert you via text message and optionally email before the timeout period ends (fig. 4).
Fig. 4
iv. Notify contacts and share data
Add trusted contacts who should be made aware that you are no longer using your account. You can also share data with them if you like (fig. 5, fig. 6 and fig. 7).
Fig. 5 (the time period after which your Account will be timed-out and the auto-response message after the account is timed-out)
Fig. 6 (auto-response-do not forget to click “save”)
Fig. 6.1 (click add trusted-contact)
Fig. 6.2 (insert email address for your trusted contact and click next)
Fig. 6.3 (select data to be shared with your trusted contact)
Fig. 6.4 (prepare email for the trusted contact when receiving your data. Click “save”)
Fig. 7 (Click enable to set up the Inactive account manager)
Fig. 8 (disable the Inactive account manager)
v. Optionally delete account
If you wish, instruct Google to delete your account on your behalf.
Fig. 9 (click “yes” for “delete my account” under “Optionally Delete Account”. Click “Enable”)

Fig. 10 (select either Delete Account + Content or Delete your entire Google profile)
Fig. 11 (select your choice as outlined in the Figure bellow. Click “Delete Google account”)
Any questions can be submitted to: dan@e-crimeexpert.com
Additional information can be found at: http://www.e-crimeexppert.com
Hit the “subscribe” button in order to be notified when new videos and Articles are posted on this blog
Do you know what is your child’s age requirement to sign up online?
As the Internet permeates every aspect of the economy and society, it is also becoming an essential element of our children’s lives. While it can bring considerable benefits for their education and development, it also exposes them to online risks such as access to inappropriate content, harmful interactions with other children or with adults, and exposure to aggressive marketing practices.
Children online can also put their computer systems at risk and disseminate their personal data without understanding the potential long-term privacy consequences.
In addition, there are other risks for children using online environments, such as:
–Privacy risks
-cyber-bullying
-cyber-stalking
-age-inappropriate content
-online grooming
-identity theft
-emotional implications.
Beside support and guidance from parents when using the online environment, an appropriate mental development and understanding is important for a child when using an online platform. For these reasons, in both the United States and the European Union, a minimum age requirements for accessing the “online world” was set as a legal requirement.
E-Crime Expert thinks that the minimum age requirements a child should meet when signing up for an email account, Facebook, etc., should be a topic of interest for parents. For these reasons, we researched the minimum age requirements on some of the most popular online sites and platforms.
The Children’s Online Privacy Protection Act (COPPA) in United States applies to the online collection of personal information by persons or entities under U.S. jurisdiction from children under 13 years of age. It details what a website operator must include in a privacy policy, when and how to seek verifiable consent from a parent or guardian, and what responsibilities an operator has to protect children’s privacy and safety online including restrictions on the marketing to those under 13. While children under 13 can legally give out personal information with their parents’ permission, many websites altogether disallow underage children from using their services due to the amount of work involved.
In the European Union, the European Commission released in January 2012, a Proposal on the protection of individuals with regard to the processing of personal data and on the free movement of such data (General Data Protection Regulation).
This Proposal has specific requirements with regards to Children. They deserve specific protection of their personal data, as they may be less aware of risks, consequences, safeguards and their rights in relation to the processing of personal data. To determine when an individual is a child, this Regulation should take over the definition laid down by the UN Convention on the Rights of the Child.
“Article 8
Processing of personal data of a child
For the purposes of this Regulation, in relation to the offering of information society services directly to a child, the processing of personal data of a child below the age of 13 years shall only be lawful if and to the extent that consent is given or authorised by the child’s parent or custodian. The controller (i.e. the person in charge with the collection, use and disclosure of personal data) shall make reasonable efforts to obtain verifiable consent, taking into consideration available technology”.
Following, are the minimum age requirements for children using different Internet websites or Social Networking Services and other online platforms:
1. Facebook:
How old do you have to be to sign up for Facebook?
In order to be eligible to sign up for Facebook, you must be at least 13 years old.
The minimum age requirement on Facebook is more or less enforceable. Simply lying about your birthdate easily circumvents the policy.
The Children’s Online Privacy Protection Act (COPPA) mandates that websites that collect information about users aren’t allowed to sign on anyone under the age of 13. As a result, Facebook’s Statement of Rights and Responsibilities require users of the social network to be at least 13 years old (and even older, in some jurisdictions).
According to MinorMonitor, over 38 percent of children with Facebook accounts are 12-years-old and under. Even more worryingly, 4 percent of children on Facebook are reported to be 6-years-old or younger, which translates to some 800,000 kindergarteners on Facebook.
These results come from a survey of 1,000 parents of children under 18-years-old who use Facebook. The company provides a free, web-based parental tool that gives parents a quick view into their child’s Facebook use, including potential dangerous activities such as the friending of online predators, cyberbullying, violence, drug and alcohol use, as well as sexual references.
2. Google:
Age requirements on Google Accounts:
- United States: 13 or older
- Spain: 14 or older
- South Korea: 14 or older
- Netherlands: 16 or older
- All other countries: 13 or older
Some Google products have specific age requirements. Here are a few examples:
- YouTube: When a YouTube video has been age-restricted, a warning screen is displayed and only users who are 18 or older can watch it. Learn more about age-restricted videos.
- Google Wallet: 18+
- AdSense: 18+
- AdWords: 18+
3. Yahoo
When a child under age 13 attempts to register with Yahoo!, they ask the child to have a parent or guardian create a Yahoo! Family Account to obtain parental permission.
Yahoo! does not contact children under age 13 about special offers or for marketing purposes without a parent’s permission.
Yahoo! does not ask a child under age 13 for more personal information, as a condition of participation, than is reasonably necessary to participate in a given activity or promotion.
Yahoo! is concerned about the safety and privacy of all its users, particularly children. For this reason, parents of children under the age of 13 who wish to allow their children access to the Yahoo! Services must create a Yahoo! Family Account. When you create a Yahoo! Family Account and add your child to the account, you certify that you are at least 18 years old and that you are the legal guardian of the child/children listed on the Yahoo! Family Account. By adding a child to your Yahoo! Family Account, you also give your child permission to access many areas of the Yahoo! Services, including, email, message boards and instant messaging (among others). Please remember that the Yahoo! Services is designed to appeal to a broad audience. Accordingly, as the legal guardian, it is your responsibility to determine whether any of the Yahoo! Services areas and/or Content are appropriate for your child.
4. Hotmail
As on Hotmail’s Terms of Use is no reference to the age requirements to join the service, we did our own registration and it appears that 13 is the age requirement for joining Hotmail, as shown below:
I. Attempt indicating the user is 6 years old
Step 1
Step 2
Step 3
II. Second attempt, indicating the user is 13 years old.
Step 1
5. MySpace
- You must be at least 13 years old to have a Myspace profile
- If you’re under 16 years old, you’re not allowed to list your age as over 16 and make your profile public (your profile must be set to private)
- If you’re under 18, you’re not allowed to list your age as over 18
- Users under 18 are not able to make changes to their listed age
Notes & Tips
- If you break any of the above rules, MySpace will be forced to delete your profile for safety and security reasons (it’s all in their Terms of Use)
6. Skype
Skype not directly sets up an age restriction within their Terms of Use.
“Jurisdiction’s Restrictions: If the law of Your country prohibits You from downloading or using Skype Software because You are under the age limit or because the Skype Software is not allowed in Your country, please don’t use it”.
According to this, for US the minimum age requirement is 13 + (COPPA).
7. LinkedIn
PRIVACY POLICY, 18!
In terms of LinkedIn’s Privacy Policy:
”Children are not eligible to use our service and we ask that minors (under the age of 18) do not submit any personal information to us or use the service.”
8. Twitter
Age screening on Twitter
Age screening is a way for brands and others to determine online whether a follower meets a minimum age requirement, in a way that is consistent with relevant industry or legal guidelines. This makes it easier for advertisers and others with content not suitable for minors (e.g. alcohol advertisers) to advertise on Twitter.
There apparently, is now age restriction for setting up an account on Twitter (as we set it up without being asked about our age). See below:
Step 1
Step 2: Done!
For more advice on how children could stay safe online (you could also share this with your child), click here to visit the material E-Crime Expert specially created for this purpose.
Any questions can be submitted to: dan@e-crimeexpert.com
Additional information can be found at: www.e-crimeexppert.com
Hit the “subscribe” button in order to be notified when new videos and Articles are posted on this blog.
Teaching Kids About Identity Theft
Today, E-Crime Expert is pleased to introduce Nancy Parker, who is a freelance writer which loves writing articles on opinions and social awareness. Nancy is a frequent contributor for http://www.enannysource.com.
“Identity theft occurs when someone gets a hold of someone else’s personal information and poses as that person or uses that information to create their own fake identity. This information can be a full name, social security number or a bank account number“.
For children, identity theft occurs a little differently. Child identity thieves are looking for their victim’s Social Security number. Since children don’t have any credit history, it makes it easier for thieves to use their Social Security number and a false birthday to open credit cards.
Read bellow this interesting interview conducted by Michelle LaRowe:
“Identity theft is a real problem and, sadly, children are not exempt from having their identities stolen. Recently, I connected with Julie Myhre, who covers identity theft for NextAdvisor.com, and here is what she had to say.
eNannySource: How does identity theft happen?
Julie: Identity theft occurs when someone gets a hold of someone else’s personal information and poses as that person or uses that information to create their own fake identity. This information can be a full name, social security number or a bank account number. It’s usually easier for identity thieves to get information about an adult because adults have a lot of personal information about them; however, it is important to also remember that children can be victims of identity theft too. There are a lot of different ways that adults can be hacked; some of these include not having privacy settings on social media, clicking on phishing emails or pop-ups, losing a wallet, throwing away documents that contain personal information, and ATM or credit card skimming, among others.
For children, identity theft occurs a little differently. Child identity thieves are looking for their victim’s Social Security number. Since children don’t have any credit history, it makes it easier for thieves to use their Social Security number and a false birthday to open credit cards. The unfortunate part about this is that people who were victims of child identity theft don’t usually realize it until they are older and trying to apply for a credit card or loan. Thieves usually gather children’s personal information from sports team applications, school documents and any other documents that would have your child’s Social Security number on it.
eNannySource: How is it prevented?
Julie: There are a lot of different steps that you can take to prevent identity theft. One of the major ways to prevent identity theft is to sign up for an identity theft protection service. Most of these services monitor your personal information regularly and alert you if they notice any suspicious or possibly fraudulent activity. A good amount of these services also offer family plans, which will allow you to protect your whole family – including your children – from identity theft.
Some other options to prevent identity theft include shredding all documents that contain yours or your child’s personal information, checking your bank accounts and credit card statements regularly, monitoring your credit report and, lastly, knowing what you and your child post online. A lot of people don’t realize how much information they post about themselves and their family on social media. It’s fine if you want to include some personal information – such as your full name and photo – but make sure that you set your profile to private. Monitor what you and your child post on social media, and check the privacy settings regularly – at least monthly.
eNannySource: What basic things can parents teach children to avoid identity theft?
Julie: Parents should teach their children about identity theft in a similar manner that they teach them about strangers. If you think about it, it’s essentially very similar – someone you don’t know is trying to take something from you. Parents just need to teach their children that their personal information is private and they should not reveal any of it to people they don’t know. Children won’t understand the details of identity theft, so it’s important not to go into too many details. The bottom line is personal information should be kept personal, and it’s important that parents recognize that and teach it to their children.
eNannySource: What age do parents have to start worrying about identity theft?
Julie: Parents should begin to think about ways to protect their child from identity theft as soon as their child has a Social Security number.
eNannySource: Is it worth investing in some type of protection?
Julie: Yes, in most circumstances identity theft protection is worth the investment. The value of identity theft protection isn’t necessarily in the active personal information monitoring, because the reality is that people can do that part themselves. Instead, the value lies in the identity theft recovery that these services offer. In the instance that yours or your child’s identity is stolen while you’re signed up for an identity theft protection service, you are provided with all the information and tools you need to recover yours or your child’s good name. Identity theft protection services represent you when you’re dealing with the banks, credit bureaus and creditors. It lightens the load on the victim’s side and helps alleviate the nightmare of identity theft. The identity theft recovery assistance is a valuable tool to have if yours or your child’s identity is stolen.
eNannySource: What about the Internet? What are the top tips for parents of kids who use the Internet?
Julie: The most important tip that parents need to follow when their children use the Internet is to monitor what your child is doing and posting on the Internet. Have open communication with your child and make them aware that they shouldn’t be putting any personal information on the Internet – even if it’s your home address in a private message to a friend. Check in with your child and make sure these rules are being followed on all platforms, including the computer, cell phone and tablet. Check your child’s privacy settings on their phone and social media once a month to make sure the information they post on the Internet is set to private”.
*Julie Myhre is the Content Manager at NextAdvisor.com. You can review identity theft protection reviews and learn more about identity theft on the site.
To read the original post and find more about Julie, please click here.
This interesting interview nicely connects to one of E-Crime Expert‘s blog post, called: How secure is your Child’s Social Security Number?
If you have any question you could contact: dan@e-crimeexpert.com
Additional information can be found at: www.e-crimeexppert.com
Hit the “subscribe” button in order to be notified when new videos and Articles are posted on this blog.