Archive
How to download your own data from Facebook
From the same series on how to access, delete, download, transfer your data when using a major Online Social Service (Facebook) or email Provider (i.e. Google, Yahoo), today E-Crime Expert explains how a user can have access and also download his/her data Facebook collects and keeps under that particular user account.
Follow the steps bellow if you would like to have access to the data Facebook holds under your account:
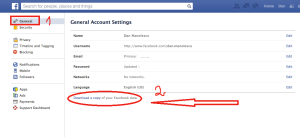
1. Log on Facebook and access the “Settings” tab. From there, click on the “Account settings” from the drop-down menu (Fig. 1).
Fig. 1.
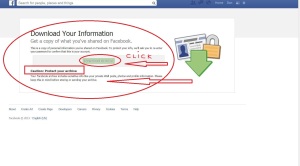
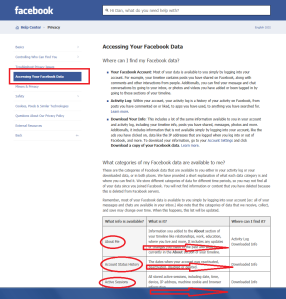
2. Navigate to the “General Account Settings” tab and click on the “Download a copy of your Facebook data” (on the bottom of the page). Fig. 2.
Fig. 2.
3. You will be promoted with a message that enables you to download your data. Also, Facebook warns the users in regards to the sensitive character of the data under their personal Facebook account. Think twice before downloading your data if you do not trust the computer you are using (i.e. Public Library, etc.). If you do trust it, just click the “Download archive” button in order to get access to your data. Fig. 3.
Fig. 3.
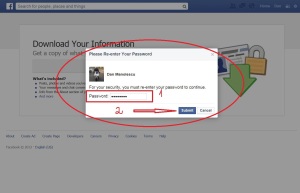
4. Next, you will need to type your password again, even though you are logged into your account (for security reasons). After typing your password, click on the “Submit” button. (Fig. 4).
Fig.4.
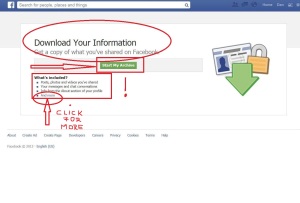
5. Again, a message is displayed informing the user which data will be downloaded: Pictures, archives, messages, timeline posts, AND MORE! (Fig. 5).
Fig. 5.
6. Also, you can manually chose to select what data you would like to download such as: photos, messages, videos, etc. For this, click here and you will be automatically redirected to another page where you could select what data you want to download (Fig.6). Or you could also click on the “And more” tab as shown in Fig.5 above.
Fig.6.
7. Now, depending on your Operating System (i.e. Windows or Apple), or your Browser (i.e. Internet Explorer or Safari) and also on the time elapsed since you last requested your data from Facebook (if ever), your data will either start downloading immediately to your computer or it will be sent to the email address associated with your Facebook account. We are explaining bellow both possibilities:
I. Data starts downloading immediately.
After clicking the “Submit” button (see Fig. 4 above), you will be prompted to save your data on your computer. Chose a location you are familiar with and also which it is neither public nor shared with other users and click “Save”. Your data will start downloading automatically. (Fig.7).
Fig.7.
II. Data is sent to the email address associated with your Facebook account.
You will be prompted with another message called “Start my archive”. Click on it. (Fig. 8).
Fig.8.
-The email address associate with your Facebook account is displayed in order for the user to confirm that this is the right email address. If so, click on “Okay”. (Fig. 9).
Fig.9.
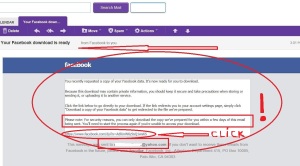
-Check your Inbox folder (under your email account) and click on the message received from Facebook. On the bottom of the message you will find a link similar to this: https://www.facebook.com/joe.doexfnr11……..Qdxwe…..rlaA9LVP. Click on it. (Fig. 10).
Fig.10.
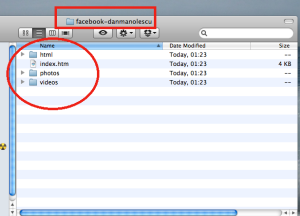
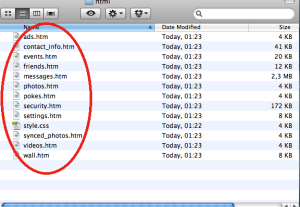
-Again, be careful and chose a location you are familiar with and also which it is neither public nor shared with other users and click “Save”. Your data will start downloading automatically. The folder with your Facebook data will look like in the pictures bellow. (Fig. 11 and 12).
Fig. 11.
Fig.12.
Any questions can be submitted to: dan@e-crimeexpert.com
Additional information can be found at: http://www.e-crimeexppert.com
To find out more about Dan Manolescu, visit his LinkedIn page here.
Hit the “subscribe” button in order to be notified when new videos and Articles are posted on this blog
Yahoo deletes IDs of inactive email accounts starting with July 15!
E-Crime Expert recently launched a series (see the first blog post here) on how you control your data stored online by different (e-mail) Service Providers. This could be done directly (by setting up an inactive account deletion time for your Google account) or indirectly (by not signing in your Yahoo account).
For those who have a Yahoo account and who have not signed in for the past year, their personal data stored under their account will be automatically deleted with no opportunity to recover it or to transfer it to anyone else by expressing their WILL as Google provides for example by offering the Inactive Account Manager tool.
Warning!
If you are not planning to have your account deleted and all your data erased (emails, pictures, chats, etc), please note that Yahoo Inc. plans to release the inactive accounts unless the current owner logs on again before July 15 (2013). After that, the (deleted) identifications will be available to all comers (as a fresh Yahoo account) and will be ready to use again in mid-August, while the data of the original user will be permanently erased!
Yahoo is resetting email accounts that have not been used for at least 12 months and issuing them to other users as they are trying to attract new users (by freeing unused email accounts) and retain current active users with IDs of their choice, the company is also giving inactive users the opportunity to retain them:
“All you have to do is log on to any Yahoo! product before July 15th. In future, these accounts will remain active by signing in at least once every 12 months, according to a Yahoo help notice, titled “We want you back.”
According to the above statement, All you have to do is log on to any Yahoo! product before July 15th, if you haven’t logged into Yahoo! for over a year, but want to keep your Yahoo! ID, and/or to log on any Yahoo! product at least once every 12 month if you want to keep your Yahoo! account active!
Any questions can be submitted to: dan@e-crimeexpert.com
Additional information can be found at: http://www.e-crimeexppert.com
Hit the “subscribe” button in order to be notified when new videos and Articles are posted on this blog
WHAT TO DO WHEN YOUR EMAIL GOT HACKED OR COMPROMISED
E-Crime Expert explains in this blog post the steps to be taken when your email or Social Networking Site has been hacked or compromised.
When someone’s friends or close contacts start telling that they are receiving emails or messages that one never sent, or when appears online content that one never posted, it could mean that another person has gained illegitimate control over this individual’s email or Social Networking Site.
If this happened, in order to limit the damage and the possibility of spreading malwares/viruses to others, firstly the passwords to all accounts that have been compromised and to other important accounts should be changed*, and also notifications to all contacts regarding that they may receive spam messages that appear to come from the compromised account, should be sent.
It could also happen that one cannot access his/her account anymore because a password has been changed.
If this happen, bellow are provided the contact details for the most popular email and Social Networking sites providers:
* Hacked account – click here:![]()
* Account is sending spam – click here: ![]()
* Hacked account – click here: ![]()
* Inaccessible account – click here: ![]()
* Hacked account – click here: ![]()
* Inaccessible account – click here: ![]()
* Hacked account – click here: ![]()
* Inaccessible account – click here: ![]()
* Hacked account – click here: ![]()
* Hacked account – click here: ![]()
TIPS:
* How to choose a strong password:
Watch video : “Creatting a strong password video tutorial”
Read blog post: “Tips for a better, stronger password”
Frequently check your account activity/log in history as explained in this blog post: “Does anyone snoop in your email account? Find out”
If you have any question you could contact: dan@e-crimeexpert.com
Additional information can be found at: www.e-crimeexppert.com
Hit the “subscribe” button in order to be notified when new videos and Articles are posted on this blog.
Does anyone “snoop” in your email account? Find out
E-Crime Expert presents today the basic tips for helping users know if their email account was accessed without authorization by someone else. In order to find out, users could use their sign-in history log or activity logs that are provided by Yahoo Mail or Gmail. Unfortunately, Hotmail does not yet offer such option.
I. Yahoo
Step 1.
Go to Account Info, located under the drop down menu when you click on your name on the upper right corner of your Yahoo page (you have to be logged on).
Step 2.
Then, you will be prompted to introduce again your password in order to Access your Info.
Step 3.
You will be re-directed to the page where all your account info are displayed.
Navigate to the right side bottom of that page to: View your recent sign-in activity.
Step 4.
Click on View your recent sign in activity box and you will be taken to your recent account log in activity that will display the place from were you loged on in the past weeks (Country and City), the IP address from where you were logged on, the Date and the Time you logged on, the Access Type (Browser) and the Event, which refers to the either log in, log out or mail access. If you would like to have a report that goes further in time than two weeks, click on View More option, on the bottom right of that page.
II. Gmail
Step 1.
Log in your Gmail account and go to your name on the upper right corner of your account. and click View Profile.
Step 2
Then you click on the Account Activity tab and you will be re-directed to another page where you could view the basic information about your all Gmail-related account such as Picasa, Mail, YouTube, etc.
Step 3.
To order your Activity report, click on the Account tab and beside you will see the last Countries you signed in your account and the exact time, you could also order your Account Activity Report.
Step 4.
After you ordered your Google Account Activity Report, from your Account page, you will receive an email Notification in your Gmail account. Open the message and click Open Access Activity report, then you have to type your password again in order to access this Report.
Alternative way for accessing your Gmail Activity History:
Step 1.
While logged in your Gmail Account, go to the very bottom-right corner of your account and click Details.
Step 2.
Then, you will be automatically redirected to another page where all your recent Account Activity will be displayed: Access Type, Location IP, Date and Time.
III. Hotmail
Unfortunately Hotmail does not provide such a function to access your Account History or Activity Log (as you could see in the picture bellow). Although anyone could send an email to Hotmail’s reps asking for their Activity Log Report. This Report will provide users with a maximum of two weeks of their Activity Log information. Further than two weeks account activity/log in history, Hotmail says, that it will be only provided for law enforcement purpose or requests.
Any questions can be submitted to: dan@e-crimeexpert.com
Additional information can be found at: www.e-crimeexppert.com
Hit the “subscribe” button in order to be notified when new videos and Articles are posted on this blog.
Web 3.0 and privacy
In order to understand why privacy and personal data are so vulnerable in relation with the Internet and its adjacent services/platforms, E-Crime Expert developed a research study, aiming to learn what the Internet is, how it works, what Social Networking Services are and how they came into place, why SNS are so popular, how private information can be retrieved from SNS users, what is the purpose for targeting and behavioral advertising and what cloud computing is. Today, Web 3.0 is a first post in a series that aims to understand the cause in order to provide a better effect (better privacy).
E-Crime Expert believes that users’ awareness and online education help protect their privacy and personal data. For these reasons, my research interest in the use of social network services (SNS) and search engines began when I realized that many options and features of the SNS I use (i.e. Facebook) or search engines (i.e. Google), are questionable from the user’s privacy and data protection perspective. I believe that a more in depth understanding of the their functionality, usage and applications on the newly emerging Web 3.0 (also known as Semantic Web) could help users protect their private information and personal data.
Privacy and protection of personal data are increasingly discussed and analyzed by law enforcement, advocacy groups, industry and academics, legal practitioners, and policy makers. In my previous research (LLM) Thesis, I tried answer the question: if the SNS, Facebook, is in compliance with the European Union’s Data Protection Directive 95/46/EC. Furthermore, I am trying to better understand what Web 3.0 is and how operates.
With the immersion of Web 3.0 personal data and private information cannot be fully controlled. Soon (service) providers, by employing Artificial Intelligence, may be capable to predict what people want regarding a particular search query, products or services, in order to be deliver one single choice which it supposed to be the choice sought by the user. But would this be done at the expense of privacy? It’s important for policy makers and lawmakers to be aware of these challenges in order to keep up with the continuous technological developments.
What is Web 3.0?
Tim Berners-Lee (the director of the World Wide Web Consortium which oversees the Web’s continued development, also founder of the World Wide Web Foundation, and senior researcher and holder of the 3Com Founders Chair at the MIT Computer Science and Artificial Intelligence Laboratory) has described the semantic web as a component of Web 3.0.
Computer scientists see that Web 3.0 will be more application based by functioning on “non-browser applications and non-computer based devices…but… geographic or location-based information retrieval” while using Artificial Intelligence.
Short review of the web’s development:
Web 1.0
For example, Hotmail or Yahoo’s services were all about read-only content and static HTML websites. People navigated the web through link directories of Yahoo, Hotmail or AOL! A walled garden, a portal where the user stopped and “found” everything they needed (or the provider gave them). There was no choice for users to upload their content on those portals, such as pictures or videos, and also not much choice for others to use them with or without authorization (of course excluding hackers).
Web 2.0
Web 2.0 is the user-generated web content. Users are consuming as well as contributing information through blogs, vlogs, picture sharing like Picasa or video websites like YouTube, etc. Consumers, content publishers and users are continually becoming more of the same entity. The Web seems apparently open for anyone to contribute, modify and improve but actually it is not like that because these information appliances providers such as Facebook, deliver the platform, products and services of their choice in a closed-capsule form. It is also a walled garden (rather a prison which looks like a park), but better and more efficient controlled, manipulated and “supervised”.
Web 3.0.
Also known as the semantic web where the data has its own meaning in order to deliver observational, behavioral and tailored content/advertising to individuals rather than to “crowds” by using searches and preferences made by users. Web searches would generate local results for user’s geographical area and would include websites that it “thinks” the user would like to see. Seems convenient at a first glance, but it also appears to be an invasion of users’ privacy.
Web 3.0 and Privacy
In the Web 1.0, users had control over their information by exchanging it strictly over email or on web portals (Yahoo, AOL, Hotmail) to designated recipients. In Web 2.0 the users also had more or less control of their own information by choosing which account or website where they will post videos and photos, or delete and modify these photos or videos. However, in the Web 3.0 case there is no guarantee on how users’ information is monitored, retrieved, aggregated and by who and where it is used. This Web 3.0 brings the users’ web experience to a different level where the users themselves have less and less control over their information and content.
Nonetheless that the opportunities Web 3.0 could offer are promising (faster interaction, more tailored content, services/info based on geographical location etc), these opportunities also come in a package with concerns regarding users’ personal information already available on the web, and moreover that no one really knows where this information is stored (data centers), how is exchanged/transferred (cloud computing), who controls/access it (service provider and third parties?), and what those that control and access do with the users’ data. A legitimate question is (which I have no answer for): who has control over the data about our everyday lives?
Ultimately, those new opportunities that Web 3.0 offers will can be safely used when reliable methods for controlling the storage, access, usage, transfer, purpose, and privacy of the data will come into place either through regulatory measures, self-regulations, better enforcement, or privacy by design and users’ education.
For me the perspective of having a smart phone, laptop, PDA, my SNS account, a website which shares information they know about me feels threatening. Why?
Because a smart phone, laptop, PDA, website, online store, social networking platform, can know my home address, personal details, contact details, financial details, bank account number, login and password information, search queries, personal preferences (movies I like, music I listen to, restaurants I eat at, pubs I go to, close friends, etc), and even more personal details.
The Web 3.0 could make it easier for users to find what they are looking for online but also it could eventually go so far to the point where users will be showed/told what they like, how they dress, what to eat, and where to go and thus having less or even no control on their own preferences. Once providers or advertisers know someone’s preferences, they will deliver that particular service or advertising as being the user’s choice and it would then not matter what a user actually wants or prefers because the choices will be limited based on their preferences (previous online activity).
But the situation could be less dramatic than it sounds as long as the users know what to share in their online “life”. There will be less chances for one to know what a user likes to eat, watch or visit if that user will not make it public online or would share the least amount of personal preferences as possible. Of course this is not enough, as nowadays providers and advertisers seem to be following or “stalking” users online like one would physically chase a person in the real life. But in the meantime providing less or no information about ourselves has more chances for us to not be “labeled”. If this is the case with Web 3.0, I am concerned thinking about what Web 4.0 will be like.
For this reason, try to take care of your personal information and data now as a wise future investment when or if the Web 4.0 will come into place.
Stay tunned for the next post in this series which will present the history of SNS.
Any questions can be submitted to: dan@e-crimeexpert.com
Additional information can be found at: www.e-crimeexppert.com
Did you know what Web 3.0 is? What do you think about Web 3.0? Are you expecting a Web 4.0 as well?
Hit the “subscribe” button in order to be notified when new videos and Articles are posted on this blog.